n the last lesson, we discussed how storing transaction data in Merkle Trees reduces the amount of data the blockchain has to store. This is important because if nodes are required to store all transaction data at all times, then the storage requirements quickly spiral out of control and become costly. Few nodes would be able to store the entire blockchain, which reduces the network’s decentralization.
Continuing with our analysis of Satoshi’s explanation, here he expands on a concept called “simplified payment verification” (SPV).
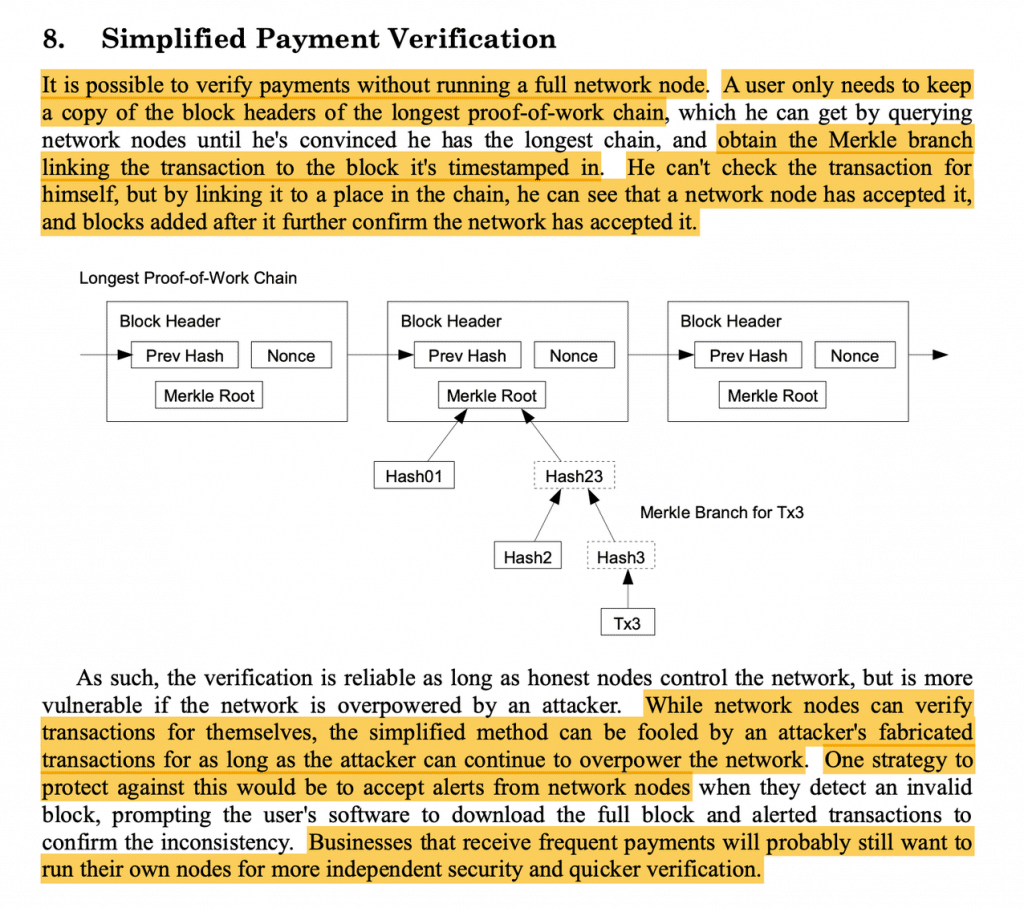
The idea behind a simplified payment verification system is to allow nodes to verify payments without needing to store the entire blockchain.
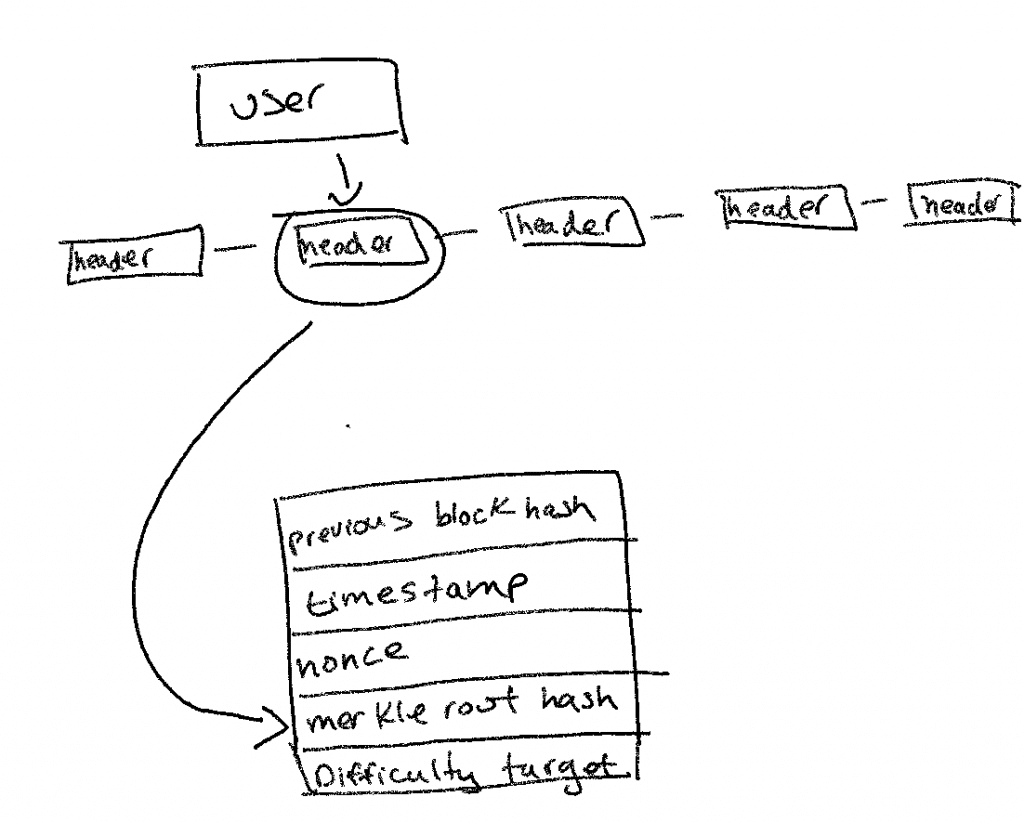
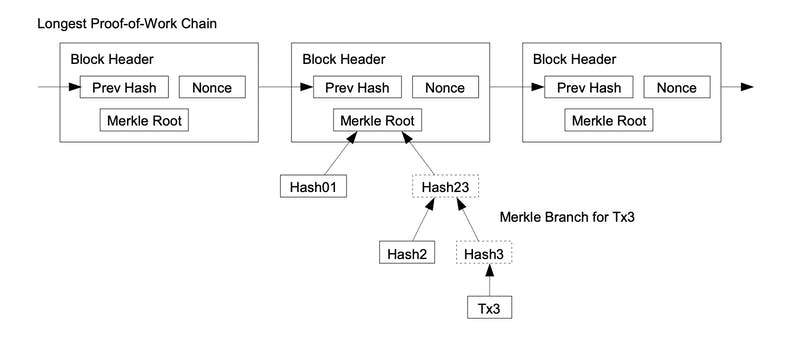
“A user only needs to keep a copy of the block headers of the longest proof-of-work chain, which he can get by querying network nodes until he’s convinced he has the longest chain, and obtain the Merkle branch linking the transaction to the block it’s timestamped in.”
You know the drill by now…Let’s break down Satoshi’s explanation. If a node wants to verify that a certain transaction happened but does not want to store the entire blockchain, it can query the Bitcoin network to receive a copy of just the block headers of the longest blockchain.
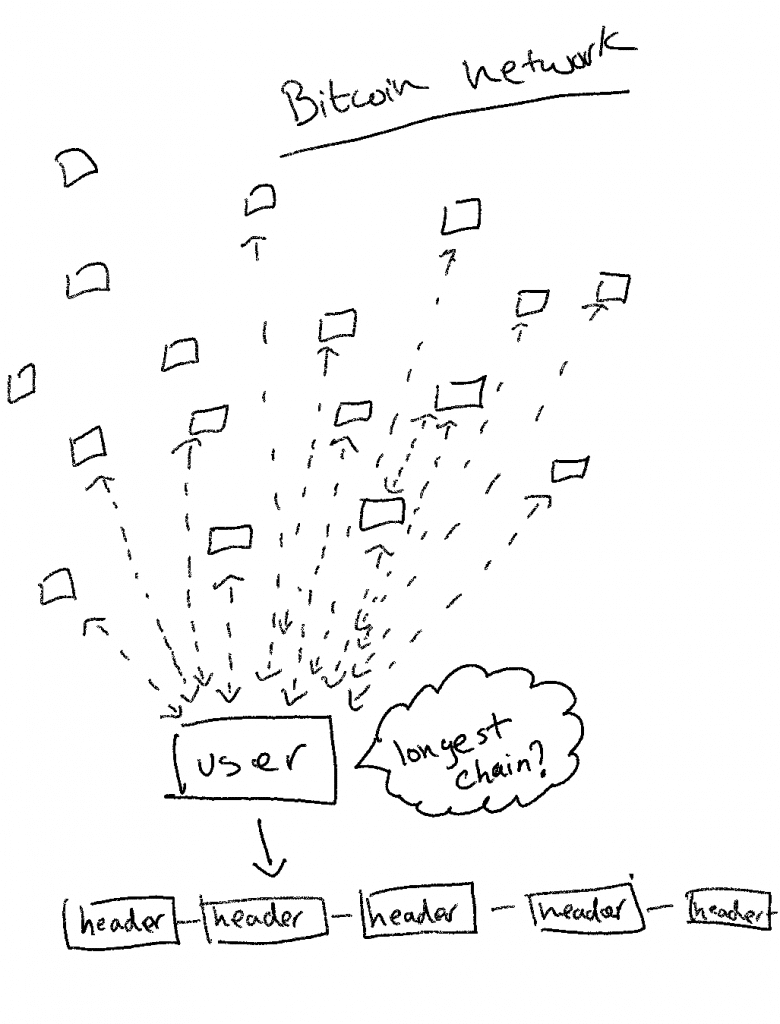
Once the longest chain is obtained, the node will look for the block that the transaction was included in.
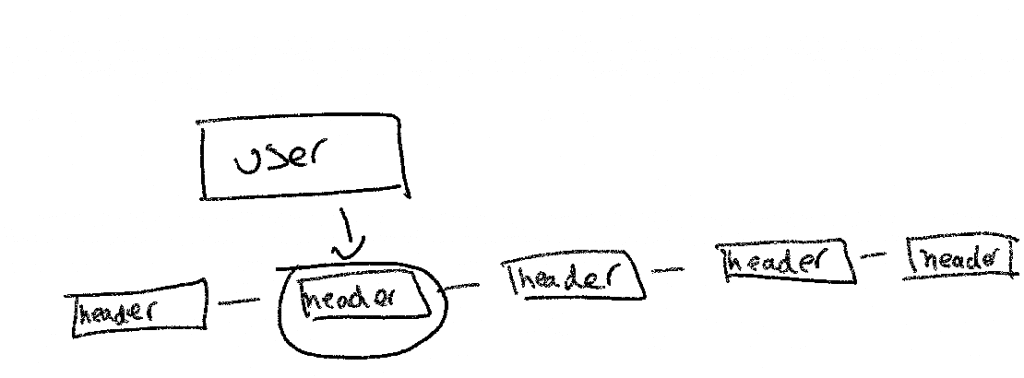
Finally, the node needs to find the Merkle branch that includes the pertinent transaction.
If a node can find the Merkle branch that includes the transaction, then that is enough to ensure the transaction is included in a block that is part of the longest chain.
“He can’t check the transaction for himself, but by linking it to a place in the chain, he can see that a network node has accepted it, and blocks added after it further confirm the network has accepted it.”
So effectively, SPV lets a node validate the transactions it cares about without having to validate all the other transactions in the network.
Satoshi then goes on to explain that this approach works so long as there are more honest nodes that control the network than dishonest nodes. This is because if an attacker has more power in the network than the honest nodes, then the attacker can easily fool the node into accepting an invalid chain as the longest chain.
“While network nodes can verify transactions for themselves, the simplified method can be fooled by an attacker’s fabricated transactions for as long as the attacker can continue to overpower the network.”
One strategy to protect against this would be to have a system where full nodes can send an alert whenever they detect invalid blocks. That way, when a user node tries to query for the longest chain block headers, it will be alerted that a certain block header that it is receiving might be invalid. It can then download the entire block and directly verify whether the transaction is in fact invalid.
“One strategy to protect against this would be to accept alerts from network nodes when they detect an invalid block, prompting the user’s software to download the full block and alerted transactions to confirm the inconsistency.”
Finally, Satoshi concludes by saying that anyone who needs strong security guarantees will likely want to run a full node in order to independently verify transactions.
“Businesses that receive frequent payments will probably still want to run their own nodes for more independent security and quicker verification.”
Once again, the devil is in the details. Many Bitcoiners believe that an SPV node is not secure enough because the node only checks the transaction it cares about. As it doesn’t check any of the other transactions in the block, theoretically the block could be invalid. Some Bitcoiners believe that most users on the network should be running a full node because:
1) It is good for the network (more full nodes = more decentralization)
2) It is necessary for the security of users, (nodes can validate addresses and transactions), and
3) It is important for the sake of privacy (SPV nodes have to request information about specific addresses and transactions, whereas full nodes have that information available to them at all times).
Other Bitcoiners believe that for practical purposes, the SPV system works just fine. Bitcoin wallets like Electrum have been using SPVs successfully for years without any problems, and they save users the hassles of maintaining a full network node. Since an SPV node is constantly querying from many different nodes for the longest chain, it can be assured that it is indeed receiving the longest chain.
Our civilization was founded on the idea of division of labor. The idea that all nodes need to be running a full node is nonsensical and too ideological.
I’m sure you have more questions than answers. Ask me in the comments section 🙂
In the next lesson, we’ll dig into the details of individual transactions. Is it all starting to make sense now? Bit by bit, we’re putting the basics of Bitcoin together!






Add Comment